It's Coming!
The arrival of Windows 11 is imminent – that much you are probably aware of. If you didn’t know, well, now you do …
Windows 11 promises to do everything that Windows didn’t do before. It’s been “redesigned for productivity, creativity, and ease.” I have no doubt that it will bring some new capabilities and features with it, but I’m not entirely sure how far the changes will extend.
Because I’m part of the Windows Insider program (I suspect many of your are, as well), I’ve been getting regular OS updates that have extended beyond standard Windows Updates for some time now. In fact, the Beta Channel that I’ve been keeping my machines in gives me early access to Windows 11 builds, and I did get an obvious Windows 11 build installed on my laptop just a couple of days ago.
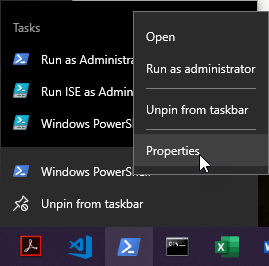
I didn’t, however, get the same build on my primary workstation. After a little checking, I realized my primary workstation had been “demoted” to the Release Preview Channel within the Windows Insider program:
The Release Preview Channel gets you features and fixes in advance, but it doesn’t get you Windows 11.
It wasn’t immediately clear to me why my primary workstation had been recategorized. I had to read through some old email to understand what had happened.
Do You Trust Me?
The reason for Threadripper’s demotion can be best summed-up this way: it was as an issue of trust.
More accurately: Microsoft couldn’t detect an active Trusted Platform Module (TPM) within my system, and so I didn’t appear to meet the minimum hardware requirements for Windows 11 seen below:
Platform security is an important topic and a concern of mine, but I need to be forthcoming with you: in the past, I really didn’t care too much about what TPMs did or how they worked. I knew that they were present in a lot of hardware (particularly laptops). If anything, that TPM hardware caused me headaches on systems that I simply wanted to setup without the need to “secure boot.” It seemed like it was never as easy to simply install an OS on hardware that included a TPM as it was on other hardware.
TPM hardware has matured over time (we’re on v2.0), and if you want to install Windows 11, you’re going to need to turn that TPM on, so you should learn a little about it.
TPM Time
It seems that TPM chips do quite a bit. If you want to turn on Windows Bitlocker these days (a good idea), the TPM chip gets involved. In essence, the TPM chip is your crypto companion, essentially enabling the encryption of information you might wish to pass across the net or store on your system. I’m sure it does more than just crypto, but that fact alone earns my respect. What a lousy job!
As you folks who follow me on this blog know, The Threadripper was built about a year ago. It naturally has a TPM module, but I hadn’t enabled it. While browsing net posts, I learned that Asus had been hard at work on BIOS updates that would enable the TPM modules for DIY folks (like myself) more easily, make them more visible, and allow them to upgrade to Windows 11. So, I did things the Asus way and rebooted my system with a USB drive that had an updated firmware image on it:

… and got my system BIOS up to v1502. It was a piece of cake, and when I went back to my Windows Insider settings (post-upgrade), it looked like I was sitting pretty:

But most importantly, it made the presence and the function of the TPM on the mainboard visible:

So if you want to be Windows 11 ready and ensure a smooth experience, make sure your TPM is visible in the system:

Because you know Windows is going to look for it!
References and Resources
- Microsoft: Introducing Windows 11
- Windows Experience Blog: Introducing Windows 11
- Microsoft: Windows Insider
- Post: The Threadripper
- Wikipedia: Trusted Platform Module
- TechRepublic: How to activate TPM 2.0 and Secure Boot in Windows 10
- Microsoft Docs: Trusted Platform Module Technology Overview
- Microsoft Docs: Bitlocker Overview